Cyber Sierra Roundtable on Managing Software Supply Chain Risk




Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.
Supply chain risk in the world of information security gains notoriety with every new breach. 2020’s SolarWinds breach is a never-ending saga, with news of impacted entities continuing to come up. Vulnerabilities in open source are another headache, with log4j dominating headlines.
How does the information security team prepare for such unknowns, with only one certainty in mind, that such unknowns exist and can come up suddenly on any given day?
A team of experts convened during the Singapore Fintech Festival 2022 to discuss supply chain risk from a cybersecurity perspective. This meeting was facilitated by Cyber Sierra in Singapore. Please find below a summary of questions, panelists, and discussion points.
- What are some impacts of third-party vendor risks? How do you manage such risks?
- Have you experienced first-hand such supply chain attacks? Can you share your learnings and experiences?
- Do you classify vendors by their potential severity of risks?
- Are you able to isolate or ring fence a problematic system or solution (from a vendor) from the rest of your systems?
- How can companies guard against misleading declarations from vendors?
- Is there a role for regulators to play in terms of enforcing certain best practices in containing supply chain risk?
- What is your opinion of a mandatory cyber insurance policy?
Panelists (Reference)
- Pramodh Rai, Co-Founder and CEO, Cyber Sierra
- Subhajit Mandal, Co-Founder and COO, Cyber Sierra
- Anagat Pareek, Advisor, Cyber Sierra
- Edwin Tan, Head of Information Security, Julius Baer
- Stephen Barnham, Global Head of Technology, Prudential
- Silvia Thom, ex-CTO, Zalora
Guarding against third-party risks amid an evolving cyber security landscape
Getting cybersecurity right can be extraordinarily complex given the constantly evolving landscape of new threat vectors and security vulnerabilities. In many cases, the weak link is human, and even senior executives have found themselves tricked through social engineering, noted Stephen Barnham, a senior technology leader in the Banking and Financials Service Industry (BFSI).
Speaking at a recent roundtable discussion organised by Cyber Sierra with IT and cybersecurity practitioners, he shared an anecdote of how a General Manager was tricked by someone purporting to be the CEO to transfer tens of thousands of dollars for a non-existent company initiative.
While the natural propensity might be to dismiss or ignore potential cybersecurity weaknesses as something that will not happen to us, Barnham urged businesses to establish a culture of awareness around cybersecurity and to make it everyone’s responsibility.
The risks from without
As the world becomes more interlinked and businesses digitalise, one growing risk would undoubtedly be from third-party organisations. At the root of this are digital systems that are increasingly integrated, including with external vendors and partners. When ignored, this can lead to a variety of cybersecurity breaches including bad actors gaining entry through them or supply chain attacks. Silvia Thom, who was formally the CTO at Zalora, shares that vendor security is a common problem.
“You send out a security questionnaire [to the third party] and you get back the answers. There’s that pressure to get the contract from the other side. And, you know, if it’s a two, three-year-old vendor, how much security could they have built up?” said Silvia.
But is third-party risk management crucial? Pramodh Rai, co-founder and CEO of Cyber Sierra thinks so. He pointed to the prevalent use of automated hacking tools by threat actors, citing the example of how some Internet-accessible databases were hacked within minutes of going live.
“Somebody somewhere has written a script that is looking for common vulnerabilities. That’s why it’s important to validate your cybersecurity posture first – because the other side is automating the process of hacking,” said Rai.
Security or speed? Choose one
But why are so few organisations paying attention to third-party risk management? According to Anagat Pareek, ex-CISO of PayTm, third-party risk management is at the bottom of priorities at most organisations mainly due to a lack of time.
“There were instances where we had to turn [vendors] away because of the lengthy onboarding time. By the time we go through the laborious security checks, it would take too much time out of the project runway. In the absence of a [better solution], it can get to the point that we miss a business opportunity,” said Barnham of the time crunch when addressing third-party risk.
But keeping everything in-house is often not the solution either. Barnham explained: “You are in a world where you want to give your developers access to open source. You want them to go to publicly available code repositories. You are contracting external developers and have a hybrid team of developers.”
For many, the result is a compromise where security is reduced to a security checklist.
“We give out access to our systems to vendors. We check the compliance of these vendors by sending them security questionnaires with checklists. If they tick ‘no’, they don’t get the contract. So, everything is ‘yes’, of course. But how do you know that each one of them is compliant?” asked Pareek.
“How are they controlling access to data? Is their data encrypted at rest and in motion? Are they PCI-compliant? We rely a lot on paperwork to answer these questions, but really, nobody has the wherewithal to go out and look at 100 vendors. It’s impossible. We need a better solution.”
A better way with Cyber Sierra
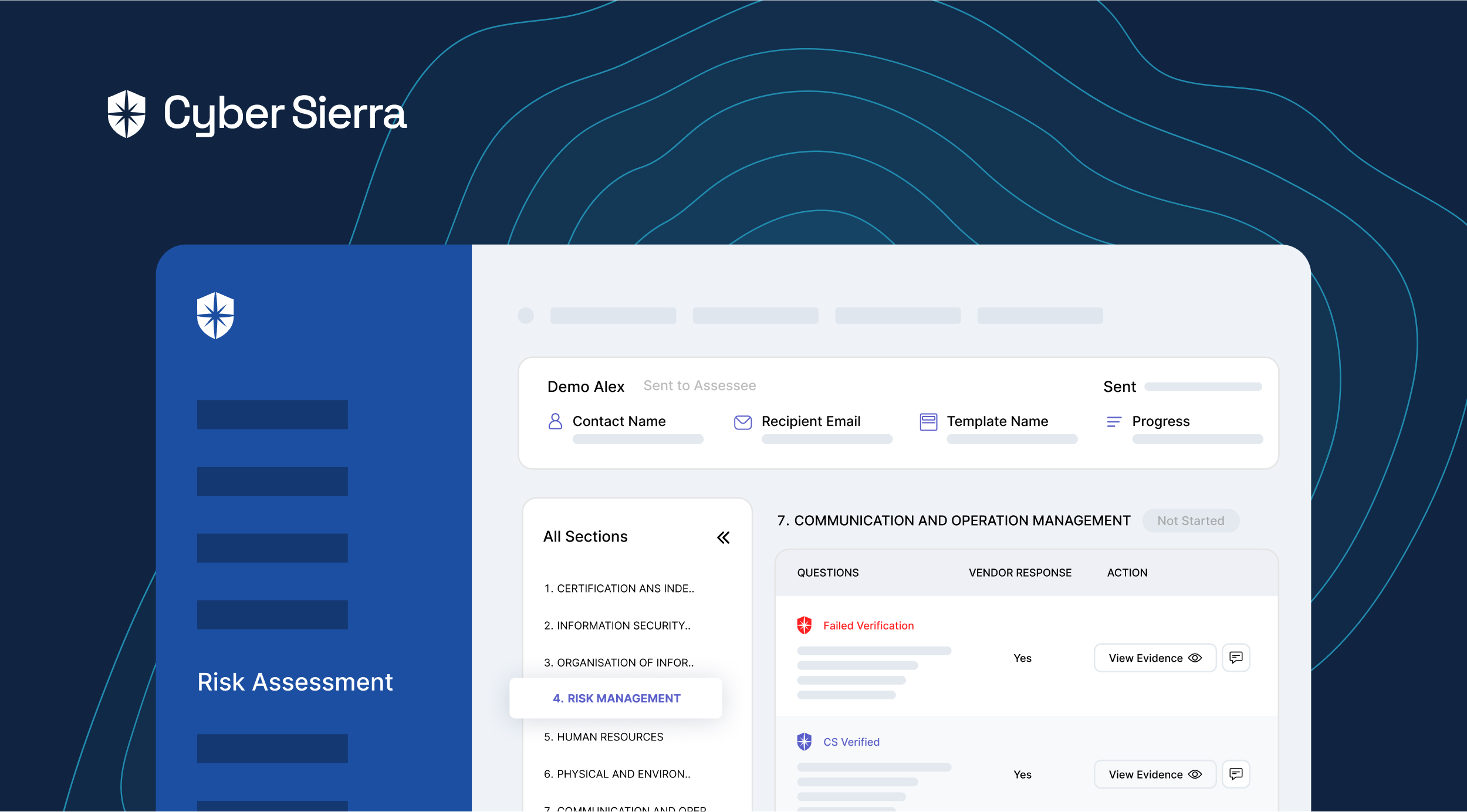
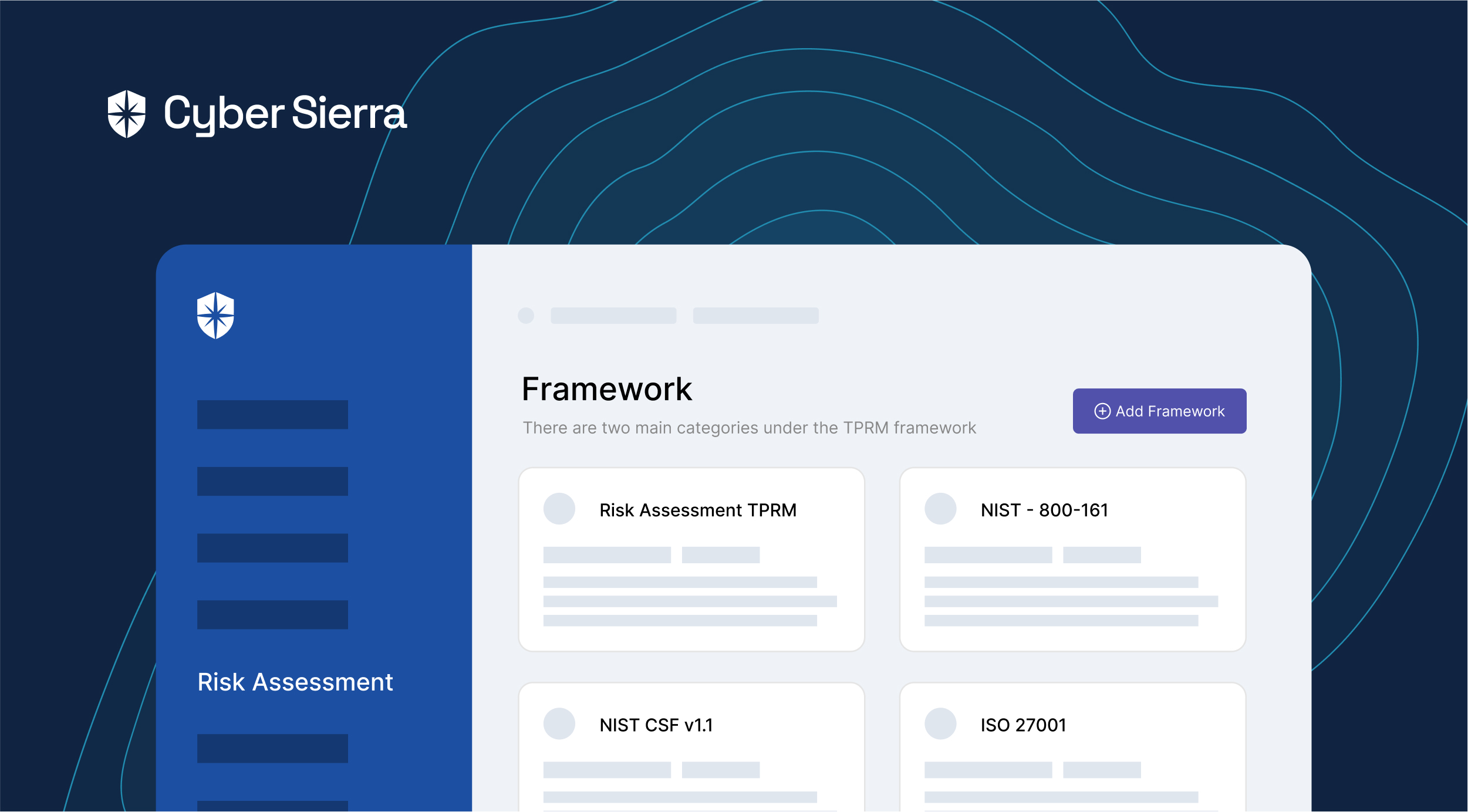
There is where Cyber Sierra can make a difference, says Pareek. “Cyber Sierra can be deployed to scan the network and upload the report. Many vendors may not know what a security vulnerability is, or what a network scan is. And they don’t want to buy another commercial solution – they are trying to build a business after all. Cyber Sierra will also help them become more secure and give the clients they work with the confidence that they’re dealing with a secure organisation. I think it’s a win-win situation.”
Edwin Tan, Head of Information Security at Julius Baer concurred: “Cyber Sierra can provide efficient due diligence of a vendor setup based on measurable criteria. This allows us to take quick proactive action in working with the vendor to address the key concerns before engaging them.”
“My environment has become so much more complicated over the last 10 years; my attack surface has become significantly broader. This is where all my attention is going. If there is a solution that enables me to connect to third parties yet gives me peace of mind about who I’m connecting to, by verifying that they are compliant to whatever standards we want to hold them to. This would help me to use my time far more efficiently,” said Barnham.
Verify and insure
Another benefit of automated checks lies in their ability to verify that a security declaration is indeed true. Barnham added: “When you have that automated tooling and knowledge that there is that automated tooling, it will disincentivise individuals from lying about their preparedness and compliance. Because now they know they are going to get caught. This allows you to get out of that vicious cycle of pointless checklists, and instead becomes a proactive collaboration.”
“Once people in the ecosystem know that you have this capability, they will not want to turn up at your doorstep, making false declarations,” Rai agreed.
And what role can cyber insurance play? Participants at the roundtable are uncertain if it should be mandatory but agreed that it can give companies a choice to mitigate risk, assuming the premium is affordable
Find out how we can assist you in completing your compliance journey.