Cloud Security




















Join thousands of professionals and get the latest insight on Compliance & Cybersecurity.
Today, we all use cloud services in our individual capacity or at work. Companies typically use cloud service providers like Amazon Web Services, Microsoft Azure, and Google Cloud to host their cloud computing services.
Cloud security is aimed at protecting data, applications, tools, and environments in the cloud through services, policies, technology, and security controls.
Cloud services providers and the customers of these providers have a shared responsibility when it comes to cloud security. Cloud services providers are generally responsible for the security of the platform, infrastructure, and applications while the customers are responsible for the security of endpoints, user and network security, applications developed on the cloud platform, and data.
A few common threats faced by companies using cloud services include:
Hijacking of account:
There are a lot of weak passwords utilized by employees which makes it easy for anyone to breach employee accounts on the cloud. Sometimes, cloud-based deployments are outside a customer’s network and accessible by anyone on the internet. Weakly configured security can enable an attacker to gain access without the organization’s knowledge
Denial of service attacks:
A successful denial of service (DoS) attack on cloud infrastructure can affect multiple companies. A DoS attack is done by flooding a target with traffic higher than the manageable level of traffic. This causes the target to shut down.
Data loss:
Loss of account access and breaches can lead to the loss of important data stored in the cloud such as personal information, activity logs, and system backups.
Protection against these threats includes:
Education on cyber hygiene
Human errors account for a significant portion of breaches and losing access to an account on the cloud can cause major breaches. Being educated on best security practices reduces this risk by a huge margin.
Maintaining data protection policies
Having data protection policies classifies different types of data based on how sensitive they are. These policies can ensure that highly sensitive data is not stored on the cloud where the risk of breaches is high
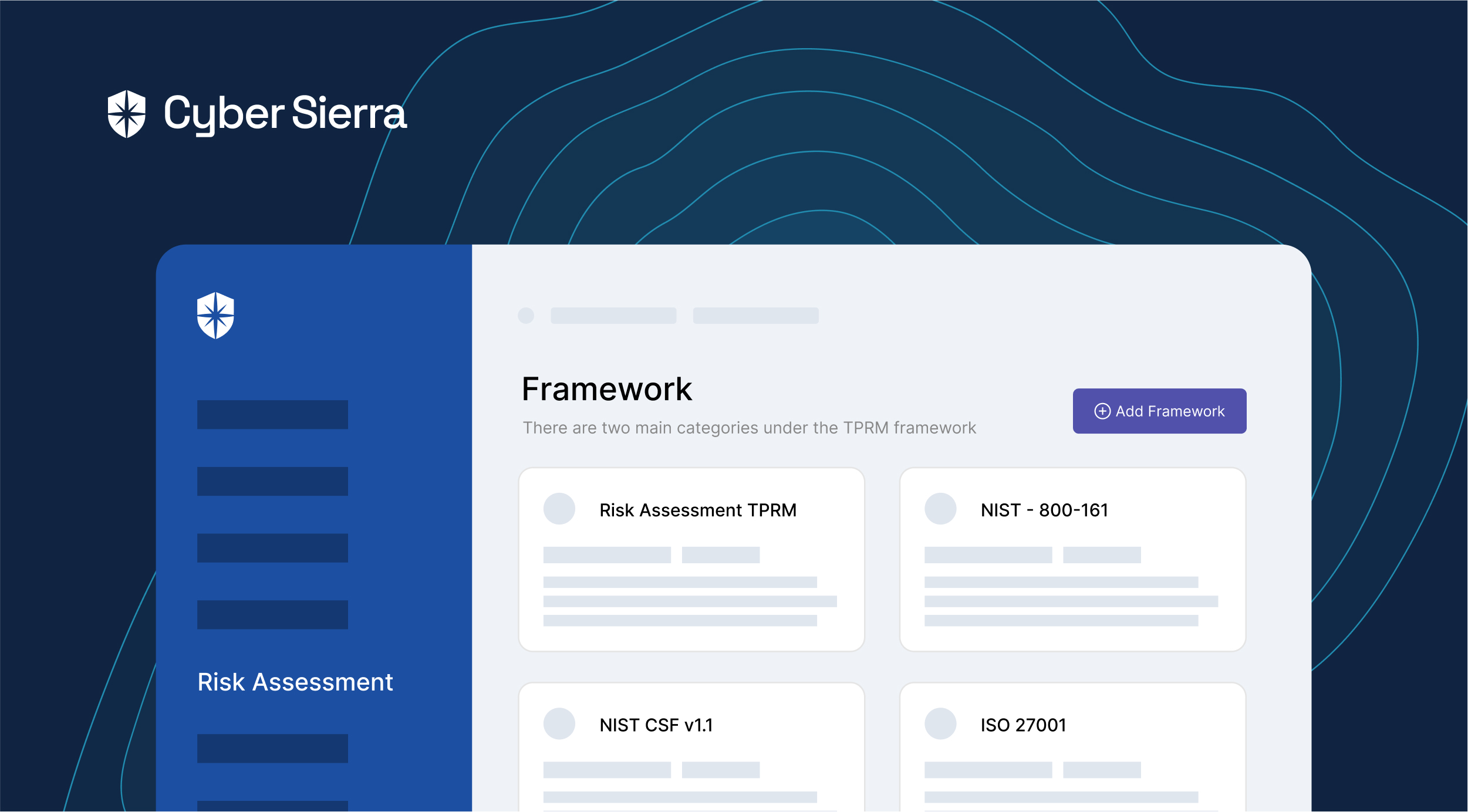
Subscribing to a reputable cloud security solution
Cloud security providers constantly update their solutions based on the latest threats and subscribing to a cloud security solution would ensure all-around protection of cloud services.
Find out how we can assist you in completing your compliance journey.